According to latest reports, the court has submitted the documents which were unsealed on Thursday. As per the details shared by a cyber security researcher, it was highly credited and it was helping it to neutralize “WannaCry”, a kind of a global ransomware attack which was recorded in the beginning of this year. The suspects were arrested basis on the unrelated hacking charges.
A U.S. based spokesperson of Justice Department has revealed that Marcus Hutchins, who was a 23-year-old from British origin, a malware researcher had gained much attention especially in May in order to detect a “kill switch”. This was effectively disabled by the WannaCry worm. It was further detained and under observation of FBI in Las Vegas on Wednesday. Also, a spokesman for U.S. Justice Department added this. Among tens of thousands of hackers, he was considered to be descended of the city and was said to be annual Black Hat as well as Def. Con conventions too. His hacking skills were well known. He could easily set codes and decodes with facing any hassles.
This incident was registered in the U.S. District Court which was located in Wisconsin. Hutchins was accused and was commonly known as “MalwareTech,” in the online space. It’s advertising, profiting and distribution remained from the malware code was recognized to be “Kronos” which got stolen using credentials via online banking as well as keeping a track on the data of credit card. During the time frame of July 2014 to July 2015 Hutchins’ was engaged in various alleged activities which were as per the impeachment. Hutchins, who had faced six counts which were in relation to Kronos. It was also indicated that there was an unknown defendant who traced on July 12. Despite all efforts being put the case got was sealed until Thursday, just a day later after he got arrested.
In Las Vegas, Hutchins got appeared before the U.S. Judge Nancy Koppe on Thursday. Dan Coe, who was a central public defender, expressed to the court that Hutchins at one point of time used to operate along with the government body previous he was charged.
On Friday afternoon the hearing got slated in order to continue and determine to know whether he is going to represent the secluded legal defender. Hutchins had no emotions to show as the charges against him were read by Koppe.
The malware was downloaded from an email which had left the system of victims’ very weak. This became easier to steal the credentials of credit card and online banking. To get money from bank accounts was not a difficult job. Thus, this activity was executed without facing any obstacles.
The accusation had also claimed unidentified perpetrator who had advertised the malware on AlphaBay platform. A dark marketplace in the international authorities had taken place in the offline space in the previous month. The investigators stated that the website would have anonymous users who can access and will be facilitated with various global traders in, firearms, drugs as well as illicit goods and hacking tools other.
The Justice Department said Kronos was used to steal banking systems credentials in Canada, Germany, Poland, France, the United Kingdom and other countries. There were systematic plans in place which can help them keep a check on so many countries in one go. They used to also keep a look on the places where there is a high potential and would smartly act through the web leaving everyone clueless to what is happening to the bank accounts. Initially, the government officials were finding very difficult to find out how it can be possible to execute such a smart plan. Despite keeping a close they were still finding it tough and have deployed more official for this investigation. Then, eventually, when they arrested the culprits they got to know the entire game plan and how big network they had created across the countries which were regulated smoothly to achieve this purpose. This was been carried out since very long time but with loads of struggle the network was shut down by government officials.
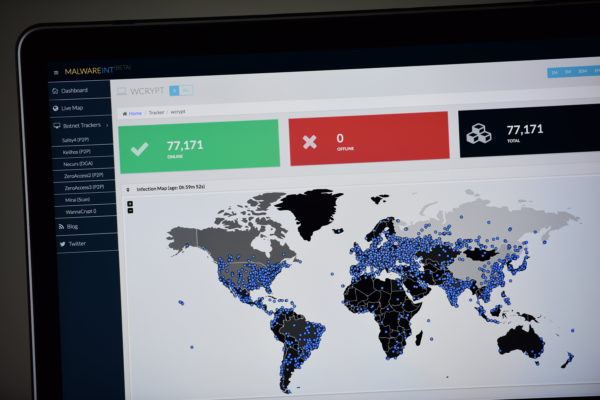
Within inside the community of cyber security, it was observed that Hutchins was a kind folk hero and was very much apparent to his role to stop the WannaCry attack. It was infected with more than hundreds and thousands of computers were aligned for this purpose. There were many disruptions seen at, hospitals, car factories, schools and shops in more than 150 countries. The investigation was done covering most of the public are so that the officials can find some clue which will help them to solve the case. They were also making sure that after this no computers were infected further as at that point this was high at risk. So was the reason that the officials were trying their best that nothing gets affected as it would have very easier for them to take over the control.
The official from Justice Department stated that he was arrested and was highly unrelated to WannaCry.
There were few security researchers as well as computer programs used by crime experts for investigation and stated they were bitten sounding very skeptical towards the charges which filed against Hutchins. The officials were trying to find a way that with help of researchers and computer program they could keep a check on him. Otherwise, tracking them would be tough as they were highly equipped with a system which hacks computers at any point in time.
Orin Kerr stated that the government would need to be determined for any other crime. A professor from George Washington University Law School and was also an expert on the subject of computer crime. It was merely generating as well as was selling a malware.
The Reuters was not able to reach out to the Hutchins. The chief executive Salim Neino was also based on Kryptos Logic, Hutchins was employed in the security firm to serve this purpose, did not reply to requests. Hutchins’ was arrested and was the first one to report this, and was traced in the Motherboard in the security website.

