Tor is one of the specialised browsers available out there. It is used by people to browse both the internet and to communicate with others in private. The thing about using the internet while keeping your online identity anonymous is that it gives you extra protection from harms that could be caused by cybercrime activities. That is why, Tor is used a lot to browse unindexed sides of the internet called the deep web, or dubbed by some others as the dark web, depending on how you see it. It earns its name for no joking reasons either, dark web is notorious for its illegal or criminal activities. Tons of malicious viruses may lurk behind the contents floating around the deeper side of the internet, and there has been a lot of scary stories associated with this obscure corner. Recently, the suspense thickens was a security expert found out mysteries behind Tor’s hidden addresses. This ‘mystery’ is an unprecedented increase in the number of hidden web addresses found in Tor’s network. What is going on?
Delving Deeper into the Mystery
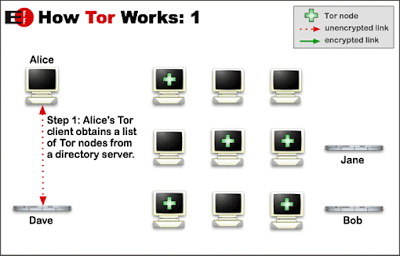
According to Prof Alan Woodward from the University of Surrey, there has been more than 25,000 .onion deep web services popped out in the recent months, and counting. He wasn’t too sure on how to explain this sudden explosion, but he posed some of the possible hypotheses anyway. A possibility he suggested is that “the boom” is probably triggered by Ricochet, a popular app that uses Tor’s service in order to make instant messaging between its users anonymous. The Onion Router, or Tor for short, has the ability to let people browsing the inter-web anonymously by routing their addresses and connections through a chain of multiple computers as well as using complicated data encryption in the process. As explained earlier, this network helps users to maintain their privacy securely. But, in every sorts of privacies, there are concerns of illegal activities being done behind the scene and all sorts of cybercrimes taking place.
“Unprecedented” Online Activity
Professor Woodward noted on his blog that this sort of thing never happened before, at least when one looked at the Tor network’s history. He suspected that there are some unprecedented things happening behind the scene, but in the meantime, it is the only thing that we know. It is difficult to pin-point things that are happening behind Tor’s scene, especially since it is created to protect people’s privacy instead of disclosing them. The thing that sparked curiosity behind this happening is that despite there’s clearly a rise of hidden network addresses, the traffic on it hasn’t been eventful at all. Deciphering the traffic content floating about the Tor network is probably something that most people will consider, but unfortunately, it is generally impossible to do so. And there’s also this concern of privacy that would be unethical to breach. There is also a possibility that this is caused by a botnet or a malware that duplicates unique network addresses when it infects someone’s computers, even though evidence for this has not yet to be found. Maybe there’s someone out there who has been experimenting on Tor, or maybe, it’s just because of the popularity of Ricochet, as suggested by Prof Woodward.
What Exactly Is Ricochet?
As explained earlier, Ricochet is an instant messaging app that uses the network of Tor in order to create a private connections between two users who wish to keep their online identity anonymous. It is very secure and this thing is achieved by not revealing either the IP addresses or the location of a user. Also, instead of a username, each of individuals who use ricochet will be given a set of unique IP addresses to mask their real ones. It has been around for quite a while, but only came into public’s positive recognition quite recently. When setting up their service, Ricochet will make unique hidden addresses, and this makes quite a logical and likely explanation for the sudden spike of Tor’s hidden addresses. But still, the mysteries behind Tor’s hidden addresses remain in the deep without concrete evidence to support it.